SaaS Products to Drive Digital Transformation
Explore our Solutions
Drive transformational initiatives by combining methods that integrate business, IT, data, and risk perspectives with Enterprise Architecture. Promote interaction and collaboration between IT and business, highlighting how your efforts will immediately affect the bottom line. Assist stakeholders in reaching a consensus on the corporate goals, gathering helpful information, and cooperating.
Enterprise Architecture
Create a strategic roadmap where you can plan future business capabilities and their related IT investments using business architecture. Optimize your current IT portfolio for cost, lifecycle, and agility. Ensure transformation projects are aligned with strategic objectives.
Business Process Management
Ensure your processes support your digital business transformation. Understand and improve the efficiency and effectiveness of your operations. Map customer journeys and identify how your processes impact your overall customer experience.
Governance, Risk, and Compliance
Get an integrated view of risks, controls, and compliance with business operations so that risk is treated as a whole and not in silos. Identify risks, implement related controls, declare incidents in a shared library and map regulatory requirements to processes and IT assets.
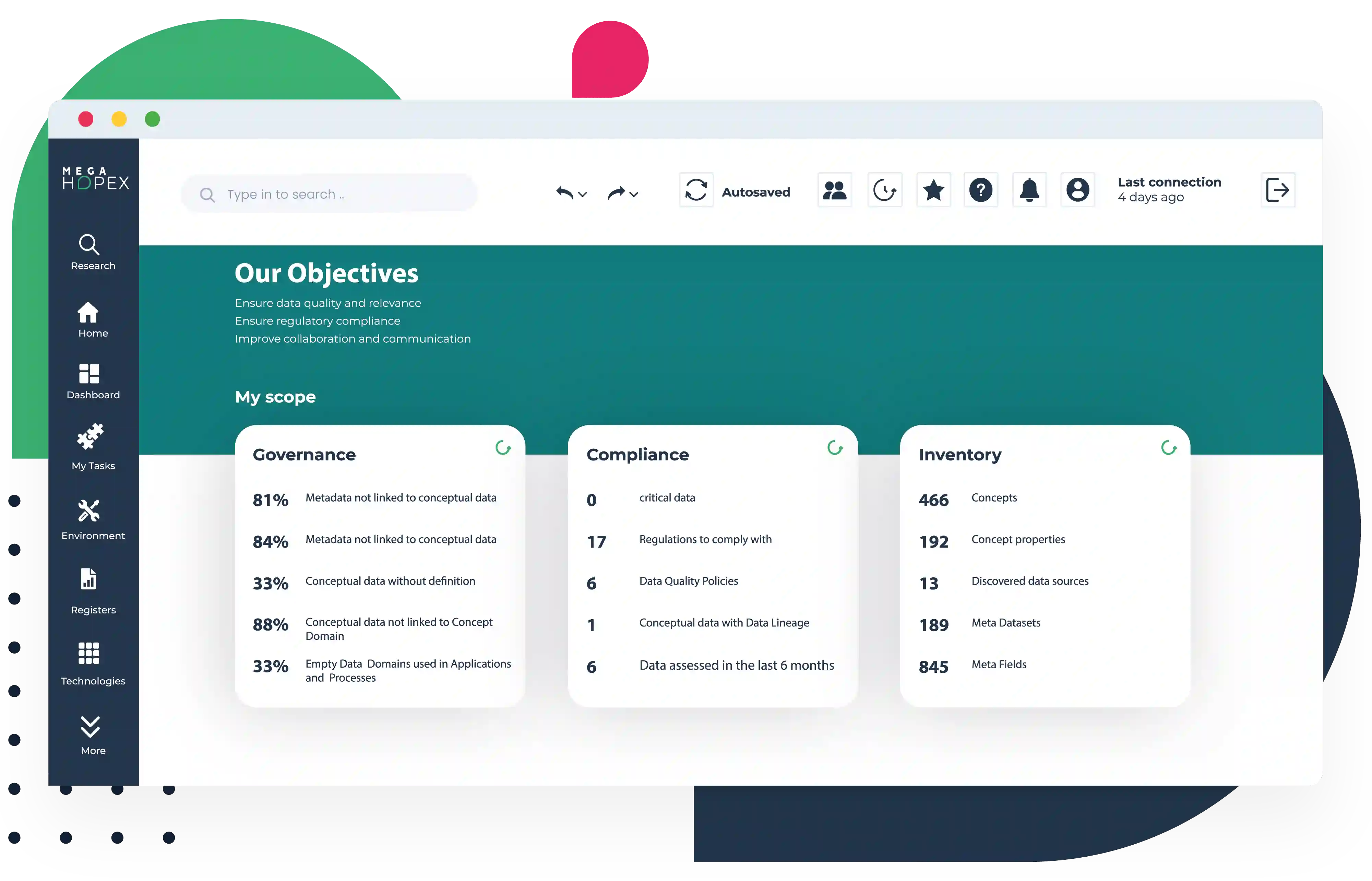
Data Governance
Use company data to address digital transformation. Increase the accuracy of your data by creating a dictionary of terms that can serve as a single source of truth. Design data using logical, physical, and conceptual data models. Map data lineage and assess data quality. Manage your organization's data compliance initiatives and ensure that guidelines are enforced.
HOPEX Platform
By breaking silos and delivering a single source of truth to all business and IT stakeholders, HOPEX enhances collaboration and alignment. Using an innovative, automated, and connected platform, they acquire actionable information to help them decide the best action.
