Digital security and enterprise architecture: Stronger together
While closely situated within the organization and closely associated with the IT department, information system security and enterprise architecture frequently develop independently in separate silos. Nevertheless, when effectively combined, they can complement one another, accelerating an organization's progress in digital transformation.
Information System security: A fragmented perspective on technological solutions
In the era of emerging technologies such as cloud computing, AI/ML, IoT, blockchain, and others, ensuring the security of Information Systems (IS) has become a prominent challenge for businesses. Forrester1 reports that 63% of organizations intend to increase their budgets allocated to information systems security. Notably, 27% of respondents consider this to be a paramount focus within their strategic objectives.
When contemplating both deliberate and unintentional threats such as malicious acts, accidents, and data loss, along with the increasing significance of digital technology in organizational growth and success, security teams engage in activities that are no longer merely essential but nearly indispensable. These activities involve addressing security aspects upstream, commonly known as "security by design," formulating a comprehensive security policy encompassing identity and access management, managing risks by identifying threats and defining controls and resilience measures, and overseeing operations through monitoring and incident management.
This can be considered as a justified deployment of forces, resulting from an approach solely focused on technology, without considering business consequences. However, the criticality of an application or a process remains fundamental to identifying and correcting digital risks in the organization.
Prioritizing threats and IS security corrective actions
While the fundamental nature of information systems security management is technical, aligning it with a strategic vision and a business-oriented approach significantly boosts its credibility.
In the realm of pinpointing and rectifying vulnerabilities, a threat deemed "significant" from a technical perspective may exert minimal influence on the company if it targets an application or a supplementary process. Conversely, any threat—regardless of its technical magnitude—demands swift consideration, as it could pose a substantial risk of destabilizing the entire organization when it impacts a core business process or application. For example, within a bank, a low-risk scenario involving a trading application should be treated with greater seriousness than a high-level threat affecting a marketing tool.
The key lies in prioritizing threats and corresponding actions based on the severity of their potential impact on the company and, more broadly, on the financial stability of the organization. This underscores the significance of the enterprise architect, who serves as a potent ally for information systems security teams by offering a cross-disciplinary perspective on business processes and elements within the information systems.
IS security in support of digital transformation
In organizations, there is a widespread consensus that comprehensive knowledge of vulnerabilities in the information system should be confined to a limited group of individuals. This practice aims to mitigate both intentional and unintentional threats originating from within the organization. As a result, the Chief Information Security Officer (CISO) and the security team typically disclose minimal information to the broader company.
Without delving into specific details, providing essential indicators of cybersecurity activities, such as the risk level associated with technologies, to enterprise architects can empower them to make informed decisions and expedite the digital transformation of the entire organization. Indeed, in scenarios like two cloud migration projects, having visibility into the "health and security" status of targeted applications can aid in prioritization. By prioritizing the migration of the less secure application, potential financial and reputational repercussions following a cyberattack can be mitigated.
While digital transformation holds paramount importance and the imperative to uphold the security of associated information systems is pressing, organizations frequently encounter budgetary limitations in this realm. Nonetheless, through collaborative endeavors, enterprise architects and CISO teams can harmonize their efforts and streamline the budgets earmarked for digital initiatives. This collaboration ensures that the organization attains a dependable, secure, and sustainable acceleration in its digital endeavors.
Enterprise Architecture Related Content
Shift from a documentation tool to an operational tool and accelerate business transformation
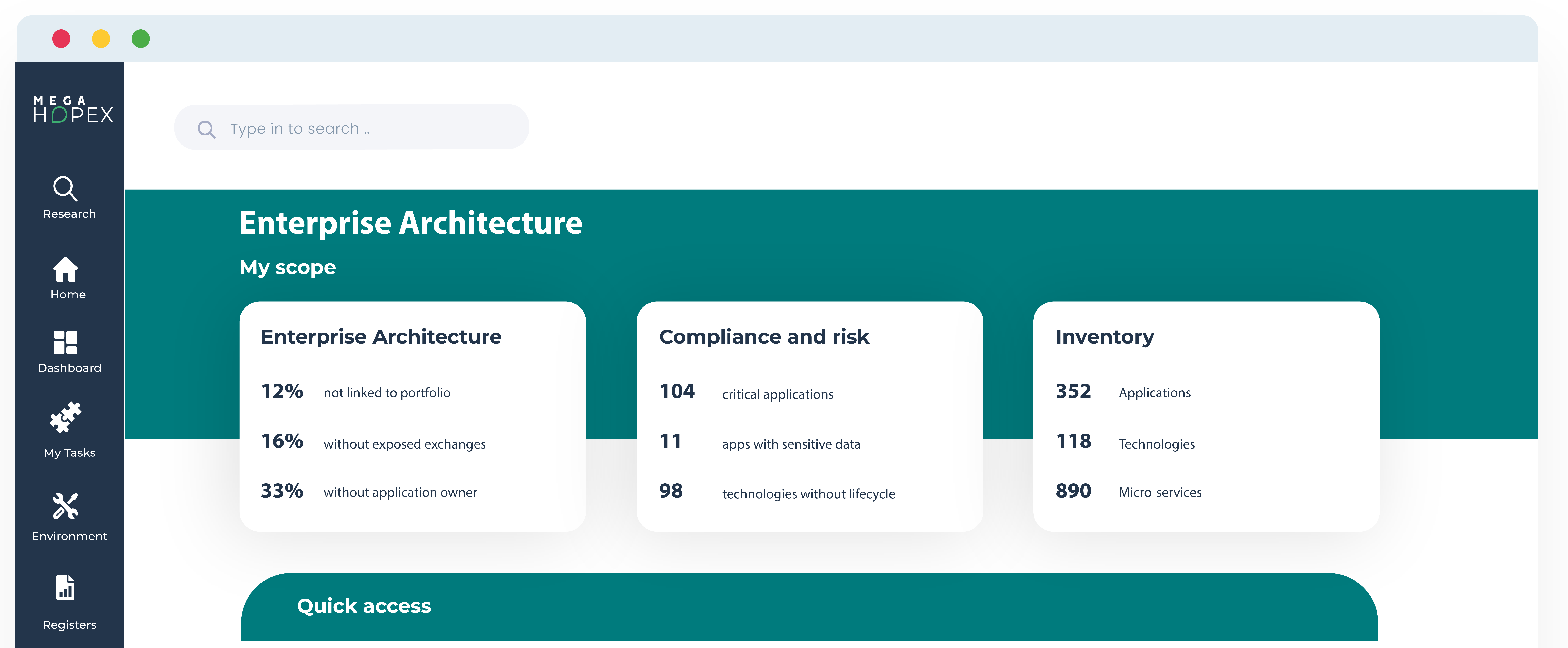
MEGA HOPEX for Enterprise Architecture
Request a demonstration of HOPEX for EA, and see how you can have immediate value of your projects.